Part 1: Using Wireshark for network traffic analysis Wireshark is a free and open-source packet analyzer. It is used for network troubleshooting, analysis, software and communications protocol development, and education. Wireshark runs on Linux, macOS, BSD, Solaris, some other Unix-like operating systems, and Microsoft Windows. There is also a terminal-based (non-GUI) version called TShark. Wireshark, …
Continue reading “ICT338e: Wireshark is a Free and Open-source Packet Analyzer: Information Security Challenges in Smart Computing Assignment, SUSS”
The post ICT338e: Wireshark is a Free and Open-source Packet Analyzer: Information Security Challenges in Smart Computing Assignment, SUSS appeared first on Assignment Help Singapore No 1 : Essay & Dissertation Writers, SG.
Part 1: Using Wireshark for network traffic analysis
Wireshark is a free and open-source packet analyzer. It is used for network troubleshooting, analysis, software and communications protocol development, and education. Wireshark runs on Linux, macOS, BSD, Solaris, some other Unix-like operating systems, and Microsoft Windows. There is also a terminal-based (non-GUI) version called TShark. Wireshark, and the other programs distributed with it such as TShark, are free software, released under the terms of the GNU General Public License.
You will use Wireshark to analyse network traffic for attacks. Depending on the OS of your machine, download and install Wireshark from this link.
Question 1
- Cheryl the system administrator has discovered malicious reverse shell connection activities while performing a routine check on her company web server’s log. She has managed to retrieve a Wireshark capture of the malicious network activities for further investigation. Apply the use of Wireshark and analyze the given network traffic ICT338 2020 ECA Q1a.pcap and answer all the questions below.
- What is the web server’s IP address?
- What is the attacker’s IP address?
- What are the transport layer protocol and port number used for the reverse shell connection?
- What are the Operating System and the version running on the web server
- What is the name of the malicious script used to perform the reverse shell connection?
- Salah the network administrator has discovered suspicious activities while performing a check on his company router’s network log. He has managed to retrieve a Wireshark capture of the suspicious network activities for further investigation. Apply the use of Wireshark and analyze the given captured network traffic ICT338 2020 ECA Q1b.pcap and answer all the questions below.
- What is the attacker’s IP address?
- From the captured traffic [packet number 1-17], provide details on the type of attack, objective, technique, and tool used by the attacker. Analyze and evaluate the packets from packet number 64 onwards.
- What is the objective of the attacker?
- Provide a countermeasure and explain how the pros and cons of the countermeasure against the attack identified.
Hire a Professional Essay & Assignment Writer for completing your Academic Assessments
Native Singapore Writers Team
- 100% Plagiarism-Free Essay
- Highest Satisfaction Rate
- Free Revision
- On-Time Delivery
Part 2: Signature-based malware detection using regular expression
Malware has threatened computers, networks, and infrastructures since the 1980s. There are two major technologies to defend against this, but most organizations rely almost exclusively on just one approach, the decade’s old signature-based methodology. The more advanced method of detecting malware via behaviour analysis is gaining rapid attraction but is still largely unfamiliar.
Signature-based malware detection is used to identify “known” malware. In computing, all objects have attributes that can be used to create a unique signature. Algorithms can quickly and efficiently scan an object to determine its digital signature.
When an anti-malware solution provider identifies an object as malicious, its signature is added to a database of known malware. These repositories may contain hundreds of millions of signatures that identify malicious objects. This method of identifying malicious objects has been the primary technique used by malware products and remains the base approach used by the latest firewalls, email and network gateways.
Signature-based malware detection technology has several strengths, the main being simply that it is well known and understood – the very first anti-virus programs used this approach. It is also speedy, simple to run, and widely available. Above all else, it provides good protection from the many millions of older, but still active threats.
You will use PCRE (Perl Compatible Regular Expressions) to write simple programs to detect malware based on given signature patterns. Refer to the document below for a summary of the PCRE syntax. You can also go to https://regex101.com/ for an online testing environment.
Question 2
TWO (2) different malware has been released recently by hackers. For each of the malware, apply a regular expression to detect the signature of the malware among the FIVE (5) given malware signatures. Provide the regular expression used for each of the malware and screenshot of the detection process. Screenshots must be provided from the command prompt of your computer.
- Malware C has a signature consisting of seven to nine leading lowercase alphabets excluding the alphabets b,f,h,j,r,y,z, followed by an optional number ranging from 2 to 7. After this, there are at least four, but not more than six uppercase alphabets. An exclamation mark optionally follows, after which the signature will end with an uppercase B, F, G or Z. Example of a malware C signature looks like ” ctllola3GUMQG!G”, ” xpmmueo7JCPURDB” or ” sxdgcvcxDTVSNZ”
- Malware D has a signature consisting of at least two, but not more than seven leading numbers, followed by one or two hyphens. A lowercase alphabet excluding the vowels optionally follows, after which follows at least one but not more than three alternating pairs of characters consisting of either upper or lowercase of alphabets “J” and “K”. The malware signature may optionally end with a “#” or “@” symbol. Samples of malware signature include “59-jk”, “3488488–jKJkJK#” and “507–dJK@”.
Part 3: Smart Computing
Question 3
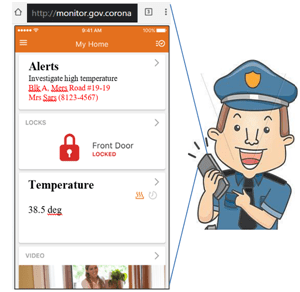
Due to the COVID-19 situation, the city of Corona is calling for a proposal for a Quarantine Monitoring System (QMS) in everyone’s home to keep track of those who are under home quarantine. QMS needs to keep track of the person’s health parameters such as temperature, heart rate, and whether the person has left the house without authorization. Once an abnormal situation occurs, QMS will send an alert to the police which is nearest to the location for investigation. QMS must be accessible by authorized users anytime and anywhere.
Using concepts of smart computing which you have learned in this module, propose a design which will satisfy all the given requirement. Assess the merits of your design, as well as critique any other potential issues such as security and privacy of data.
- Demonstrate your design in a diagram showing all the required components/devices taking into consideration the above requirements.
- Explain how the various components of your design can work together seamlessly to provide the requirements needed by the Corona Government.
- After the implementation of QMS, a policeman receives an alert on his mobile phone QMS app on a potential situation for further investigation shown in Figure Q3(c) below.
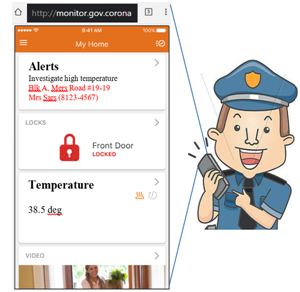
Based on the given diagram showing what he is seeing immediately after receiving the alert, assess potential security issues with the QMS mobile app, and critique on how security can be improved.
The post ICT338e: Wireshark is a Free and Open-source Packet Analyzer: Information Security Challenges in Smart Computing Assignment, SUSS appeared first on Assignment Help Singapore No 1 : Essay & Dissertation Writers, SG.